Developer Attribution & Investigation Context
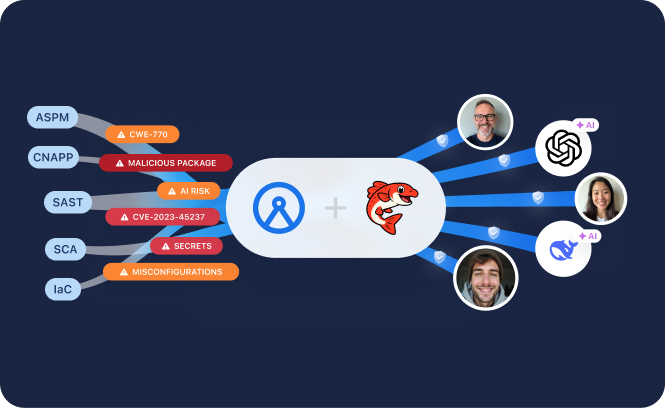
Associate Security Findings with Developer and Agent Activity
Archipelo links security scan results to identifiable developer actions and related SDLC events — across human developers, AI copilots, and autonomous agents — establishing structured context for investigation and analysis.
Attribute Security Scan Results
Most security tools identify vulnerabilities in code. Archipelo establishes developer attribution by linking security scan results to identifiable actions and pull requests — whether produced by a human developer, AI copilot, or autonomous agent.
Security scan results from integrated scanners are associated with:
- Developer-attributed actions across humans, copilots, and agents
- Pull requests and approvals
- Timestamped repository and execution events
This attribution establishes a structured record showing how findings relate to identifiable code changes and developers responsible.
Unified Event Context Across Software Creation
Archipelo maintains a time-ordered record of attributed events and associated security scan activity, including:
- Human, AI, and agent actions
- Security scan executions and results
- Related SDLC and execution events
This consolidated record establishes provenance for investigation, reporting, and audit documentation.
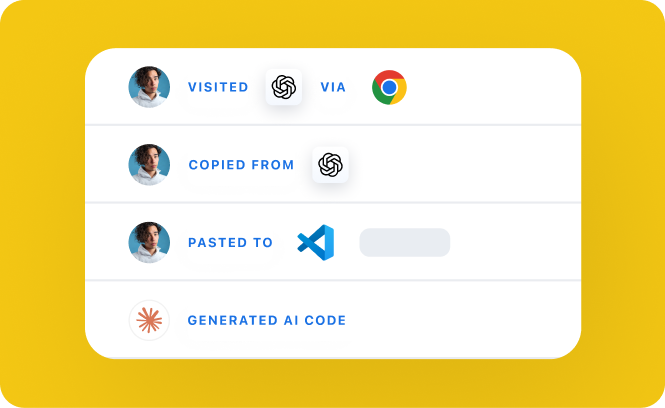
Incident Investigation & Context Reconstruction
When security issues are identified, historical context is required to examine how they relate to prior code changes and developer actions. Archipelo maintains a time-sequenced record linking security scan results to identifiable actions and associated events.
Using this record, teams can:
- Verify the sequence of related changes across humans, copilots, and agents
- Review affected pull requests and repositories
- Support post-incident analysis and documentation
Archipelo supplies upstream creation context for structured incident investigation.
Get Started
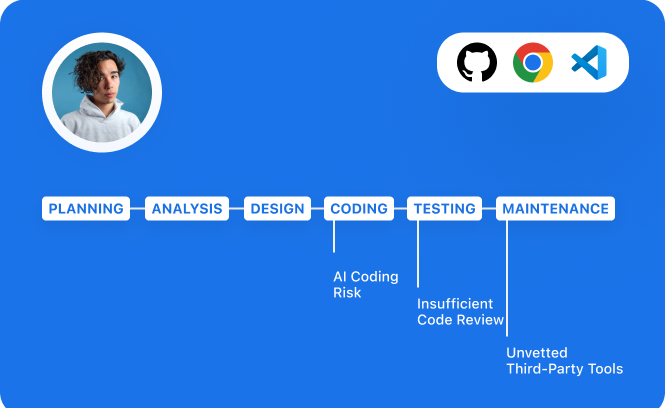
Verify how your software was produced — across human developers, AI copilots, and agents. Archipelo provides the system of record for execution attribution, security, and governance across software production.
Request a Demo